SANS SEC642 - Advanced Web App Penetration Testing
I was just lucky enough for work to send me to a SANS course in Vegas (at Caesar's no less, where Caesar lives) because a member of our team had previously booked the course and then left the company. SANS has a great refund policy and would have refunded the course minus $300. We decided that the skill set was still needed on the team so it was worth transferring the credit instead of forfeiting the $300.
Which Class To Take?
I really struggled with which class to take. I knew that I either wanted to take SEC542 (the intro web app penetration testing class) or SEC642 (the advanced version). Having just come off of completing my OSCP and having taken other security classes that covered web app pen testing, I was really trying to avoid taking another class where I learned how to make alert boxes appear with XSS (<script>alert('1')</script>) and enter ' or '1'='1 into login fields. I spend about 2 weeks going back and forth asking friends, Facebook groups, Reddit, and even the course instructors on Twitter (thanks @adriendb and @eric_conrad for the quick replies). In the end, I decided that what I had learned previously and in OSCP has prepared me to take the advanced course.
'Advanced' AKA Relevant
The class started with a review/intro section and lab. This lab felt like it was just at the right skill level for me and made me feel very comfortable with my decision to take this particular class. As we started to cover the material, I quickly began to understand that by 'advanced' they really meant that the methods taught in this class were modern, relevant, and applicable to current web application penetration testing. As with all things, you have to start with the basics which is what other classes had taught me, but it would be rare to see those exact methods used in today's modern web apps. The methods taught in SEC642 were very relevant and I felt very confident that I would see these vulnerabilities in my job and in other penetration testing avenues.
By far the most interesting (and difficult) portion of the class was the day dedicated to cryptographic attacks. Each of these attacks basically blew my mind and highlighted the many reasons why you should NEVER roll your own crypto implementation. Understanding these attacks required analysis and the bit level so naturally, it took a while to fully understand these attacks (if I even do), but their relevance was clear. The rest of the syllabus is here.
The final day of the class concluded with a CTF event where the class split into 3 teams and battled it out. Meeting a bunch of other penetration testers and developers was awesome and learning about their different roles was educational itself. Finding out that a bunch of them had remote jobs was also very encouraging! They were a really cool group of guys and I learned a ton from them as well as the class.
NetWars
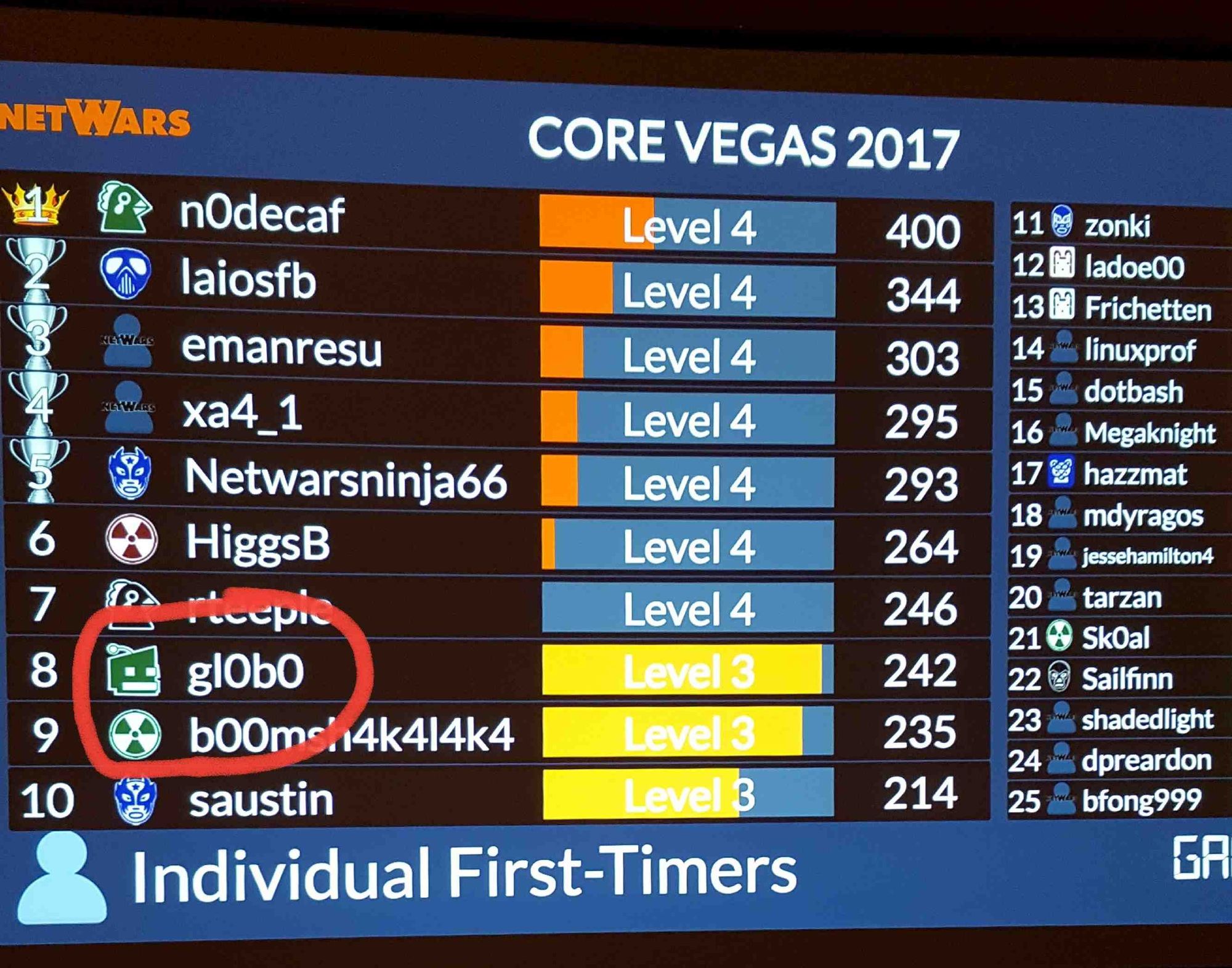
I am not sure if this is common or not but for this SANS event, registering for the NetWars event was free, so naturally I jumped on that opportunity. NetWars is essentially a hacking, forensics, and system admin contest where everyone tries to accumulate the most points. I had done NetWars once before about 4 years ago when I started my journey into cyber security in the Air Force so it was a ton of fun to do it again now that I am a bit further into my career. I had a blast and ended up in 8th place out of around 150 people who were seeing this version of NetWars for the first time (the top 7 got coins and an invitation to the national competition). I learned a few cool things from the hints in the questions and really had to expand my knowledge on at least one question. I recommend doing a NetWars event any opportunity you get...they also had free beer)
Bottom Line
Overall, I had a blast at the course and would recommend it to anyone who has a basic understanding of web app pen testing and knows how to use and interception proxy like Burp pretty well. I am sure I missed a few things from not having taken SEC542 but overall for the $5,500 price tag on a SANS course, I feel like I got my money's worth out of this class. I am not sure I would have felt the same with SEC542.
Thanks SANS and Adrien for the great class.