Hacking and Skydiving
Well I was lucky enough to get to go to a Con (Conference) again this year. I went to DEFCON last year but this year decided to go to a smaller Con to see what that was like. Based on a co-worker's recommendation, I decided to go to CactusCon in Phoenix, Arizona. Truth be told, I was also hoping to get a last minute camping slot at Havasupai Falls but that turned out to be hopeless (hopefully next year!). I also got to spend a day skydiving...but more on that later.
The Con

CactusCon started out pretty awesome because entry was free, although you could pay $45 to get the badge, a shirt, and some other swag. On the first day, they ran a CTF that they had labelled on their website as "beginner to intermediate". I decided to do the CTF after the guy running it said that the challenges would range from easy to extremely difficult and he was not lying. The content mostly focused on web application stuff, which was a good fit for me after my recent {SEC 642 - Advanced Web App Pen Testing](GHOST_URL/sans-sec642-advanced-web-app-penetration-testing/) course. Some of the stuff was fairly basic, like simple SQL injection. But each category had a graduated points scale that took the same category and progressively made it more difficult. They even had some man-in-the-middle challenges that required connection to a physical switch.
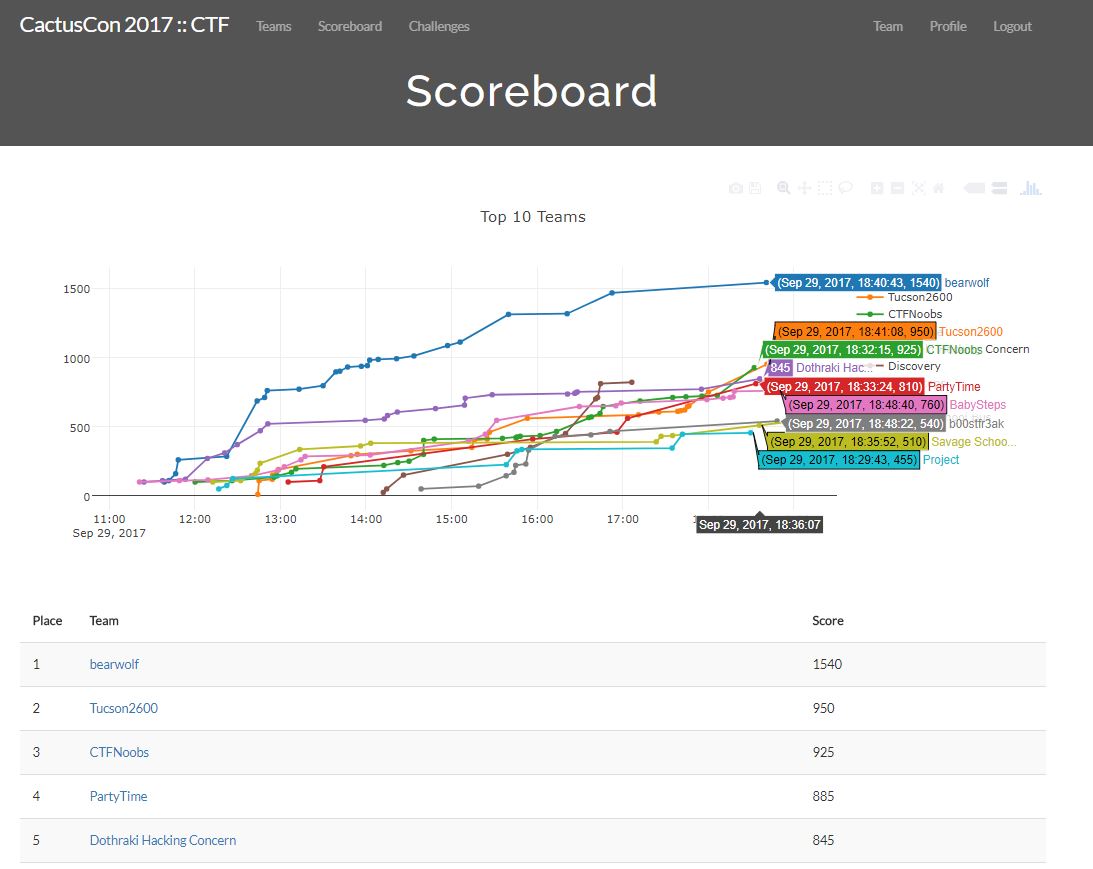
Overall, the CactusCon team ran a great CTF which great content. Particpating was a ton of fun and my partner and I (Dothraki Hacking Concern) ended up in 5th place out of 41 teams. Though we were close on a couple challenges that would have given us 100 more points.
252 flags submitted across 72 challenges by 41 teams - good times! @CactusCon #cactuscon #CTF
— Mike McCambridge (@realn0j) September 30, 2017
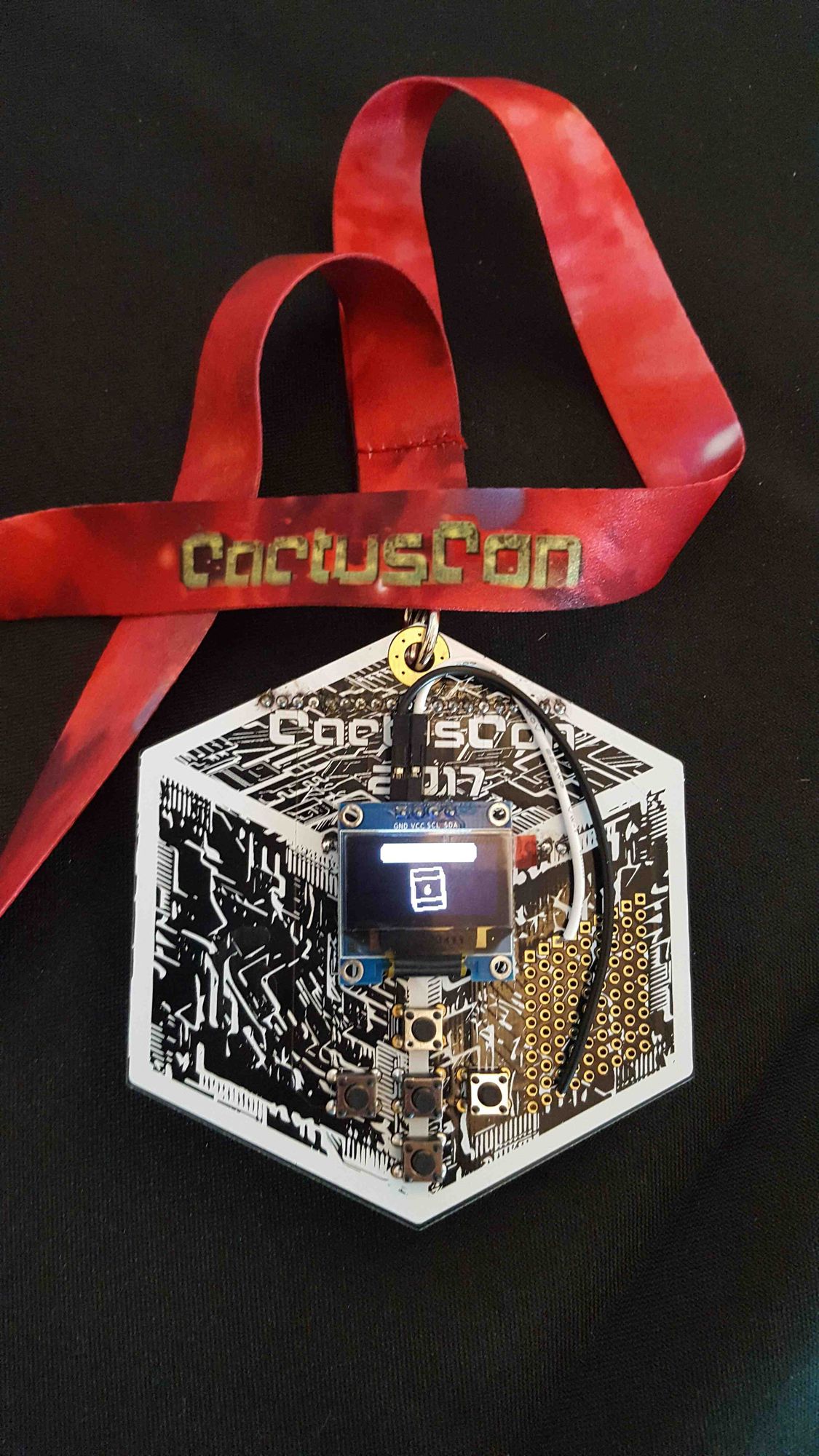
The next day I spent the morning working on the super cool badge; and by working on I mean really working on my solder, de-solder, re-solder skills. Needless to say, this was quite the learning experience. The badge is a tiny Wi-Fi and Bluetooth scanner made from a WemOS Board.
After that I attended talks on operationalizing threat intel, chaining web app vulnerabilities together, a talk on offensive and defensive PowerShell, and a talk on making production ready tools. All of these talks were good, with my favorite being the threat intel one as the speaker really tried to remove the buzz-wordiness of threat intel and turn it into some actionable data. His best point was to stop delivering IOCs to analysts that they simply do not have tools to detect (process and service names are useless if you do not have the right Windows logs or host agents).
Overall the Con was very well ran and I would recommend it to anyone who is in the area next year. I was lucky enough to also have a late flight the next day so I rented a car and headed down to Skydive Arizona in Eloy to visit the worlds most famous dropzone.
The Dropzone

Skydive Arizona is somewhat of a Mecca for skydivers, so when I knew that I was an hour away, I had to make it happen. They have a gear store, massage therapist, skydiving school, a full restaurant and bar, RV park, hotel, pool, and obviously a lot of airplanes. They also have load organizing on the weekends so I hooked up with the free-fly group and did (after a solo to get the lay of the land) an 8-way, 13-way, and another 8-way. The weather was great and the jumping even better.
It was a great weekend to combine a couple of my passions. I just wish the family had been there to join.